- Joined
- Jan 8, 2019
- Messages
- 56,623
- Solutions
- 2
- Reputation
- 32
- Reaction score
- 100,455
- Points
- 2,313
- Credits
- 32,750
6 Years of Service
76%
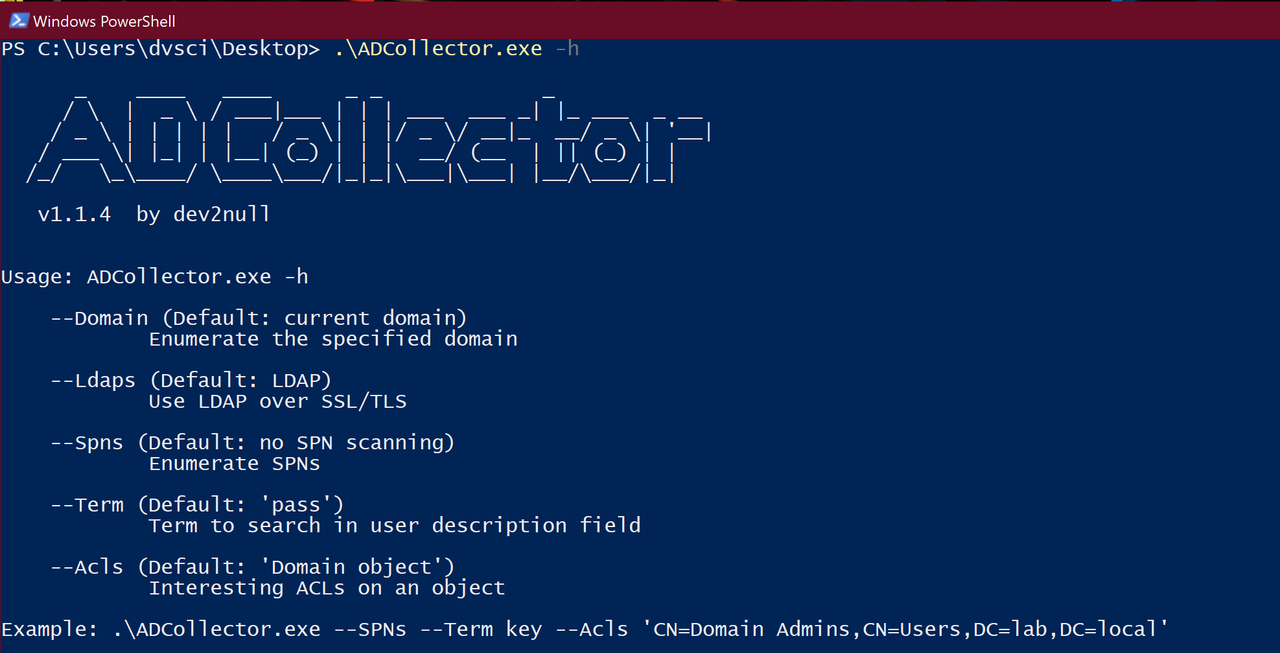
ADCollector is a lightweight tool that enumerates the Active Directory environment to identify possible attack vectors. It will give you a basic understanding of the configuration/deployment of the environment as a starting point.
Notes:
ADCollector is not an alternative to the powerful PowerView, it just automates enumeration to quickly identify juicy information without thinking too much at the early Recon stage. Functions implemented in ADCollector are ideal for enumeration in a large Enterprise environment with lots of users/computers, without generating lots of traffic and taking a large amount of time. It only focuses on extracting useful attributes/properties/ACLs from the most valuable targets instead of enumerating all available attributes from all the user/computer objects in the domain. You will definitely need PowerView to do more detailed enumeration later.
The aim of developing this tool is to help me learn more about Active Directory security in a different perspective as well as to figure out what’s behind the scenes of those PowerView functions. I just started learning .NET with C#, the code could be really terrible~
It uses S.DS namespace to retrieve domain/forest information from the domain controller(LDAP server). It also utilizes S.DS.P namespace for LDAP searching.
Enumeration
Current Domain/Forest information
Domains in the current forest (with domain SIDs)
Domain Controllers in the current domain [GC/RODC] (with ~~IP, OS Site and ~~Roles)
Domain/Forest trusts as well as trusted domain objects[SID filtering status]
Privileged users (currently in DA and EA group)
Unconstrained delegation accounts (Excluding DCs)
Constrained Delegation (S4U2Self, S4U2Proxy, Resources-based constrained delegation)
MSSQL/Exchange/RDP/PS Remoting SPN accounts
User accounts with SPN set & password does not expire account
Confidential attributes ()
ASREQROAST (DontRequirePreAuth accounts)
AdminSDHolder protected accounts
Domain attributes (MAQ, minPwdLength, maxPwdAge lockoutThreshold, gpLink[group policies that linked to the current domain object])
LDAP basic info(supportedLDAPVersion, supportedSASLMechanisms, domain/forest/DC Functionality)
Kerberos Policy
Interesting ACLs on the domain object, resolving GUIDs (User-defined object in the future)
Unusual DCSync Accounts
Interesting ACLs on GPOs
Interesting descriptions on user objects
Sensitive & Not delegate account
Group Policy Preference cpassword in SYSVOL/Cache
Effective GPOs on the current user/computer
Restricted groups
Nested Group Membership
Changelog v2.0
1. Complete Rewrite (more extensible)
2. Add Interactive Menu with command line choice
3. Use direct API call to enumerate Trust relationship
4. Update Applied GPO Enumeration with Security Filtering and WMI Filtering (WMIFilter needs to be checked manually)
5. Add LDAP DNS Record Enumeration
6. RunAs: Run ADCollector under another user context
7. Flexible SPN Scan, DNS Records, Nested Group Membership, ACL Enumeration
8. Add NetSessionEnum, NetLocalGroupGetMembers and NetWkstaUserEnum
To see this hidden content, you must like this content.