- Joined
- Jan 8, 2019
- Messages
- 56,623
- Solutions
- 2
- Reputation
- 32
- Reaction score
- 100,456
- Points
- 2,313
- Credits
- 32,750
6 Years of Service
76%
AutoSploit
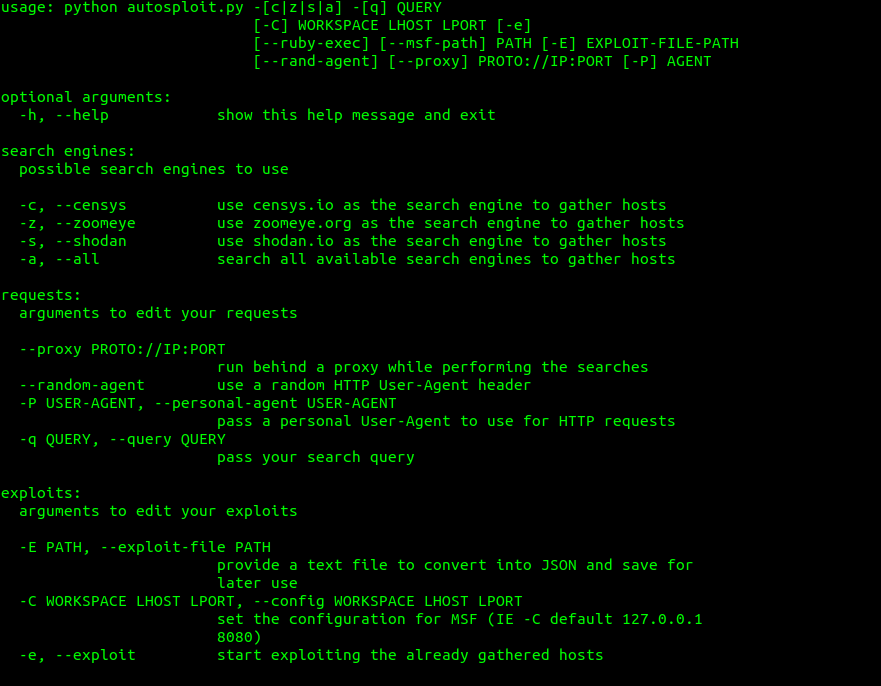
As the name might suggest AutoSploit attempts to automate the exploitation of remote hosts. Targets can be collected automatically through Shodan, Censys or Zoomeye. But options to add your custom targets and host lists have been included as well. The available Metasploit modules have been selected to facilitate Remote Code Execution and to attempt to gain Reverse TCP Shells and/or Meterpreter sessions. Workspace, local host and local port for MSF facilitated back connections are configured by filling out the dialog that comes up before the exploit component is started
Operational Security Consideration
Receiving back connections on your local machine might not be the best idea from an OPSEC standpoint. Instead consider running this tool from a VPS that has all the dependencies required, available.
The new version of AutoSploit has a feature that allows you to set a proxy before you connect and a custom user-agent.
Changelog v3.0
Features
- New Terminal. Now also supports;
- Custom Commands
- Command Histor
- Native binary execution (/bin & /sbin)
- Host file backup support
- Options to renew or reset API tokens
To see this hidden content, you must like this content.