- Joined
- Jan 8, 2019
- Messages
- 56,612
- Solutions
- 2
- Reputation
- 32
- Reaction score
- 100,454
- Points
- 2,313
- Credits
- 32,640
6 Years of Service
76%
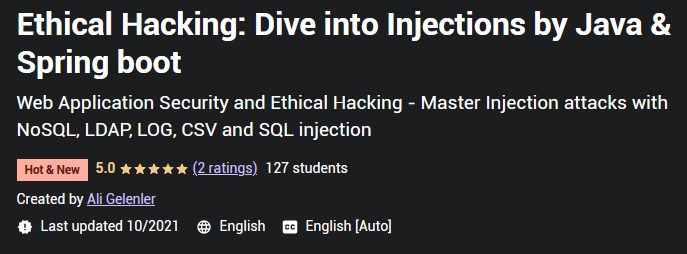
Web Application Security and Ethical Hacking - Master Injection attacks with NoSQL, LDAP, LOG, CSV and SQL injection.
What you'll learn
Ethical hacking with injection attacks
Web security
Secure coding
SQL Injection with PostgreSQL
NoSQL Injection with MongoDB
LDAP Injection with OpenLDAP
LOG Injection
CSV Injection
Spring security Form login authentication
Spring Data JPA
Spring Data MongoDB
Spring LDAP
Spring Validation
Description
Are you a Java web developer and want to write secure code? Do you want to learn Ethical hacking and Web application security? With this hands-on injection attacks course you will start learning web security using one of the top vulnerabilities of OWASP Top 10 list. Injection attack is still listed in top 3 attacks in the OWASP Top 10 and it is important to prevent against injection attacks to develop secure web applications.
As part of the blue and red security teams,I have a practical knowledge and I am here to help you learn the injection vulnerability in detail.
In this course, you will focus on different type of injection attacks;
SQL Injection
NoSQL injection
LDAP injection
LOG injection
CSV injection
Ethical hacking and Web application security are the two important subjects of Cyber Security field and having practical knowledge about Injections will enable you to better understand the security concepts and make a quick start.
In this course I will follow defense-in-depth principle and apply multiple solutions to each vulnerability to secure the web application in multiple layers.
I will follow a hands-on approach. You will not only learn how to exploit an application using different kind of injection attacks, but also develop the vulnerable applications from scratch in which you will have a common web login module with spring security form login authentication, and separate applications for SQL, NoSQL and LDAP injections.
The applications will be developed using Java and Spring boot along with the most used data sources, such as PostgreSQL for SQL Injection, MongoDB for NoSQL injection and OpenLDAP for LDAP injection.
In each section there will be;
Development of the vulnerable web application using Java, Spring boot and Spring security
Hacking of the application with various attack payloads and with Ethical hacking examples
Protection steps and the implementations to prevent injection attacks
At the end of the course you will understand the different type of injection vulnerabilities, perform injection attacks against the vulnerable web applications you have developed, and learn how to protect your applications against the injection attacks using various techniques such as,
Validation and sanitisation using white list approach
Parametrised queries with prepared statements
Escaping output
Using secure trusted libraries
Error handling and logging
General coding practices
If you want to skip the development and only perform the hacking of applications, you can jump into the injection lectures and download the source code provided in the resources section of that lecture. Be aware that you will still need to install PostgreSQL for SQL Injection, MongoDB for NoSQL injection and OpenLDAP docker container for LDAP injection. You can see how to install and configure these data sources in the beginning lectures of each injection section.
Requirements
Knowledge of Java
Basic knowledge of Spring Framework
Basic knowledge of SQL
Basic knowledge of Web application development
Who this course is for:
Developers keen on web security, ethical hacking and secure coding
One wants to dive into injection vulnerability with different attack types
One likes to learn with a hands-on approach
Code:
https://www.udemy.com/course/secure-coding-dive-into-injections-with-java-spring-boot/
To see this hidden content, you must like this content.