- Joined
- Jan 8, 2019
- Messages
- 56,623
- Solutions
- 2
- Reputation
- 32
- Reaction score
- 100,456
- Points
- 2,313
- Credits
- 32,750
6 Years of Service
76%
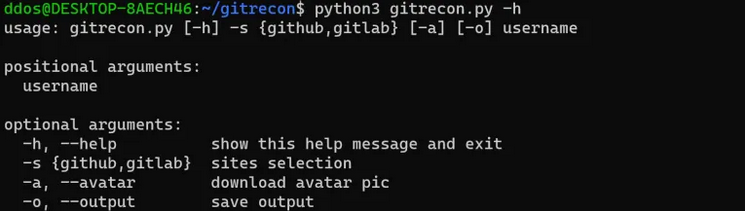
OSINT tool to get information from a Github or Gitlab profile and find user’s email addresses leaked on commits.
How does this work?
GitHub uses the email address associated with a GitHub account to link commits and other activity to a GitHub profile. When a user makes commits to public repos their email address is usually published in the commit and becomes publicly accessible, if you know where to look.
GitHub provides some instructions on how to prevent this from happening, but it seems that most GitHub users either don’t know or don’t care that their email address may be exposed.
Finding a GitHub user’s email address is often as simple as looking at their recent events via the GitHub
To see this hidden content, you must like this content.