- Joined
- Jan 8, 2019
- Messages
- 56,623
- Solutions
- 2
- Reputation
- 32
- Reaction score
- 100,456
- Points
- 2,313
- Credits
- 32,750
6 Years of Service
76%
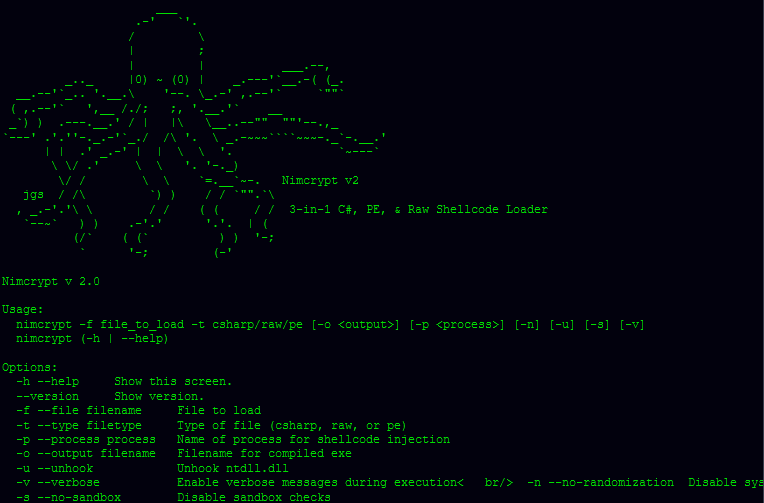
Nimcrypt2 is yet another PE packer/loader designed to bypass AV/EDR. It is an improvement on my original Nimcrypt project, with the main improvements being the use of direct syscalls and the ability to load regular PE files as well as raw shellcode.
Before going any further, I must acknowledge those who did the VAST majority of work and research that this project depends on. Firstly, I must thank @byt3bl33d3r for his Offensive Nim repo, and @ShitSecure for all of the code snippets he's publicly released. That is what the original version of this tool was created from, and the current version is no different. Particularly, the new PE loading functionality used in this tool is just an implementation of ShitSecure's recently released Nim-RunPE code. As of 3/14/22, this code also uses his GetSyscallStub code for dynamic syscall usage. I highly encourage sponsoring him for access to his own Nim PE Packer, which is no doubt a much better and more featureful version of this.
Features:
NtQueueApcThread Shellcode Execution w/ PPID Spoofing & 3rd Party DLL Blocking
NimlineWhispers2 & GetSyscallStub for Syscall Use
Syscall Name Randomization
Ability to load .NET and Regular PE Files
AES Encryption with Dynamic Key Generation
LLVM-Obfuscator Compatibility
String Encryption
Sandbox Evasion
Tested and Confirmed Working on:
Windows 11 (10.0.22000)
Windows 10 21H2 (10.0.19044)
Windows 10 21H1 (10.0.19043)
Windows 10 20H2 (10.0.19042)
Windows 10 19H2 (10.0.18363)
Windows Server 2019 (10.0.17763)
To see this hidden content, you must like this content.