- Joined
- Jan 8, 2019
- Messages
- 56,605
- Solutions
- 2
- Reputation
- 32
- Reaction score
- 100,451
- Points
- 2,313
- Credits
- 32,570
6 Years of Service
76%
pwncat is a post-exploitation platform. It started out as a wrapper around basic bind and reverse shells and has grown from there. It streamlines common red team operations while staging code from your attacker machine, not the target.
pwncat intercepts the raw communication with a remote shell and allows the user to perform automated actions on the remote host including enumeration, implant installation, and even privilege escalation.
After receiving a connection, pwncat will setup some common configurations for working with remote shells.
Disable history in the remote shell
Normalize shell prompt
Locate useful binaries (usingwhich )
Attempt to spawn a pseudoterminal (pty) for a fully interactive session
pwncat knows how to spawn pty’s with a few different methods and will cross-reference the methods with the executables previously enumerated. After spawning a pty, it will setup the controlling terminal in raw mode, so you can interact in a similar fashion to ssh.
pwncat will also synchronize the remote pty settings (such as rows, columns, TERM environment variable) with your local settings to ensure the shell behaves correctly with interactive applications such as vim or nano.
Features and Functionality
pwncat provides two main features. At its core, its goal is to automatically set up a remote PseudoTerminal (pty) which allows interaction with the remote host much like a full SSH session. When operating in a pty, you can use common features of your remote shell such as history, line editing, and graphical terminal applications.
The other half of pwncat is a framework which utilizes your remote shell to perform automated enumeration, persistence, and privilege escalation tasks. The local pwncat prompt provides a number of useful features for standard penetration tests including:
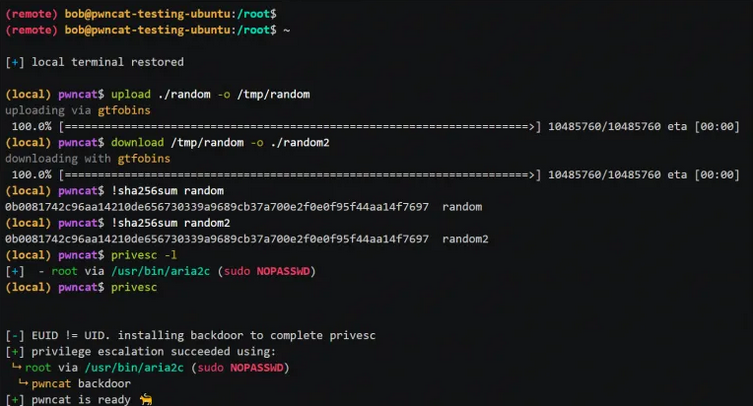
File upload and download
Automated privilege escalation enumeration
Automated privilege escalation execution
Automated persistence installation/removal
Automated tracking of modified/created files
pwncat also offers the ability to revert these remote “tampers” automatically
The underlying framework for interacting with the remote host aims to abstract away the underlying shell and connection method as much as possible, allowing commands and plugins to interact seamlessly with the remote host.
Changelog v0.5.3
Fix for argument parsing bug introduced in 0.5.2 which caused bind/connect protocols to be automatically interpreted as SSL even when --ssl was not provided.
Changed
Fixed parsing of --ssl argument (#231).
To see this hidden content, you must like this content.