- Joined
- Jan 8, 2019
- Messages
- 56,623
- Solutions
- 2
- Reputation
- 32
- Reaction score
- 100,455
- Points
- 2,313
- Credits
- 32,750
6 Years of Service
76%
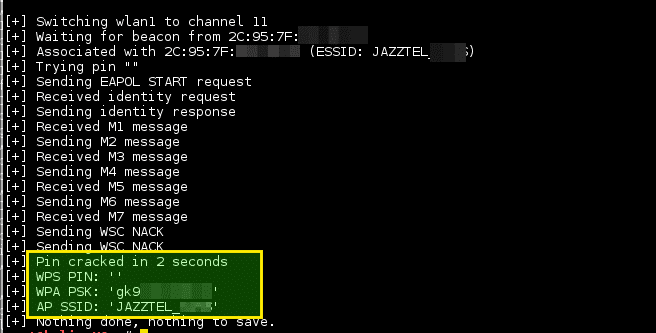
Reaver has been designed to be a robust and practical attack against Wi-Fi Protected Setup (WPS) registrar PINs in order to recover WPA/WPA2 passphrases. It has been tested against a wide variety of access points and WPS implementations.
reaver-wps-fork-t6x version 1.6b is a community forked version, which has included various bug fixes and additional attack method (the offline Pixie Dust attack).
Depending on the target’s Access Point (AP), to recover the plaintext WPA/WPA2 passphrase the average amount of time for the transitional online brute force method is between 4-10 hours. In practice, it will generally take half this time to guess the correct WPS pin and recover the passphrase. When using the offline attack, if the AP is vulnerable, it may take only a matter of seconds to minutes.
Changelog v1.6.6
several improvements have been made:
improved bruteforce mode using .wpc save files.
automatic pixiewps pin retrieval and live injection in current session if pin is cracked before the timeout happens,
experimental uptime command line switch -u
lots of bugfixes and improvements
To see this hidden content, you must like this content.